Quick Summary
We introduce a variant of the Hidden Number Problem in which the unknown noise terms are drawn from a fixed finite set and generate a lattice solution.
This is part of our series on Practical Hidden Number Problems for Programmers:
*These links are paywalled. (It’s how I’ll afford grad school lol)
Part 1: Quantum Computing and Intro to Hidden Number Problems
Part 2: Increasing Lattice Volume for Improved HNP Attacks
Part 3: Hidden Number Problems with Multiple Noise Holes
Part 4: Hidden Number Problems with Chosen Multipliers
Part 5 (we are here): Hidden Number Problems with Chosen Errors
As usual, you can code alongside the Google Colab Notebook or the GitHub repo.
1.0 Introduction
The term hidden number problem refers to the challenge of recovering a secret hidden number given partial knowledge of its linear relations (Surin & Cohney, 2023)1.
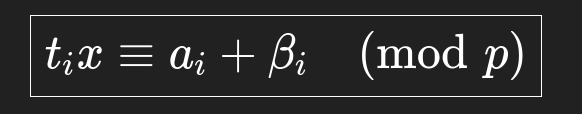
(Boneh & Venkatesan, 1996)2 introduce the linear hidden number problem and assert that lattice reduction recovers the unknown key (x) in polynomial time despite the noise term (βi) when provided known multipliers (ti) alongside known observations (ai).
We introduce the Hidden Number Problem with Chosen Errors (HNP-CE), a variant of the linear hidden number problem where the exact noise terms (βi) are unknown but shared across different relations with known weights(w).
HNP-CE arises when the Reduced Row Echelon Form of an integer matrix suffers from one or more free variables.
HNP-CE practically appears during password attacks, error-correction in satellite communications, solving Pell equations, and more generally in solving matrix systems over a finite field.
2.0 Lattice Construction and Target Vectors
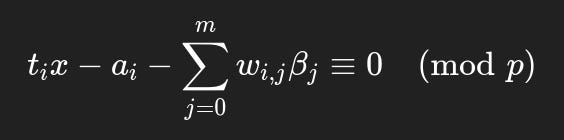
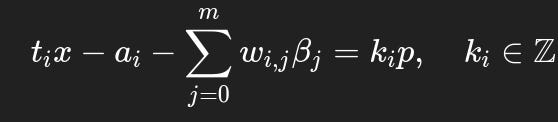
First, we ‘lift’ our relation from a finite field to the ring of integers such that:
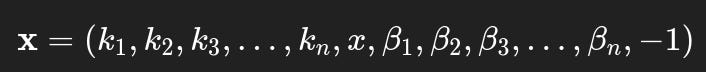
Next, we define an unknown vector x:
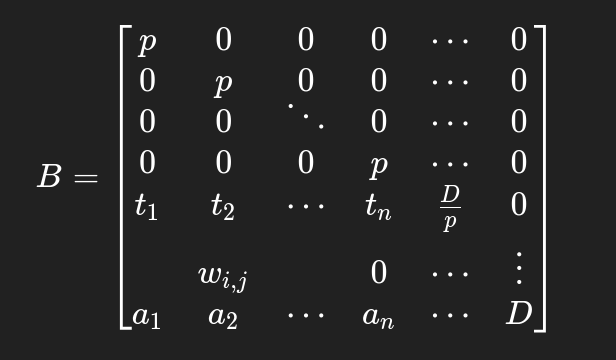
and define the corresponding basis matrix (where D is an arbitrary constant):
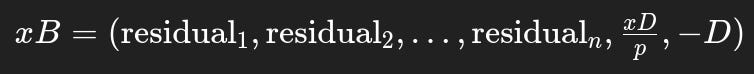
We see that the linear combination xB generates the lattice vector:
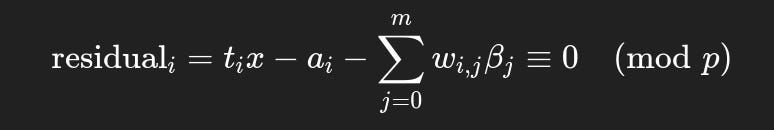
where in the optimal setting:
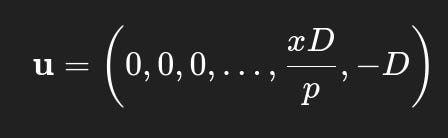
So our target vector u becomes:
2.1 Numerical Example
We cement the idea via a step-by-step example modulo the prime number 13441.
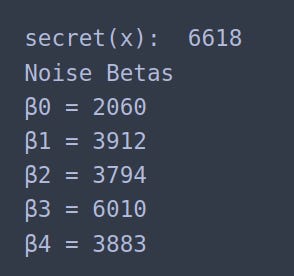
Step 1: Define a secret key (x) alongside a set of 5 possible noise terms (βi):
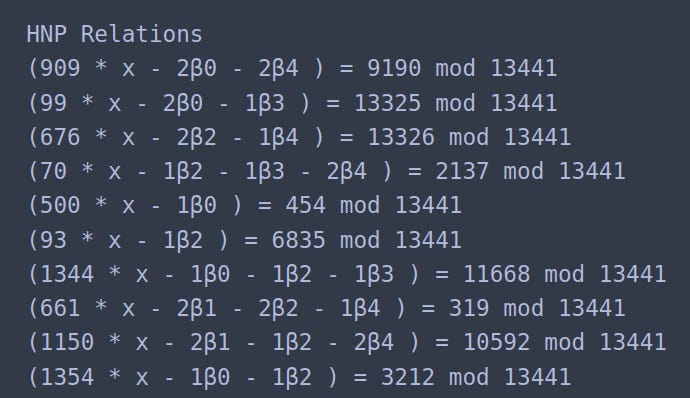
Step 2: Collect 10 relations of the form below:
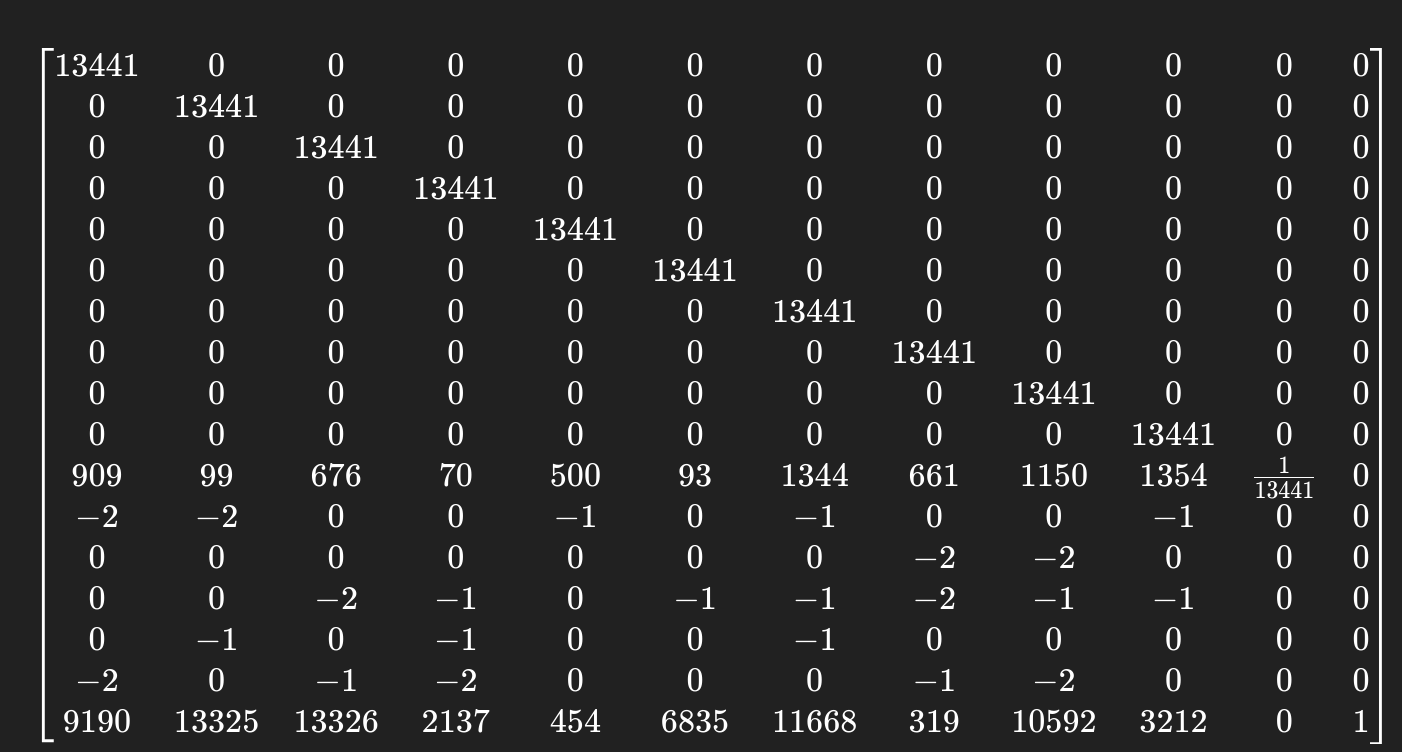
Step 3: Construct the HNP-CE lattice with D = 1 (tweak D like a hyperparameter lol):
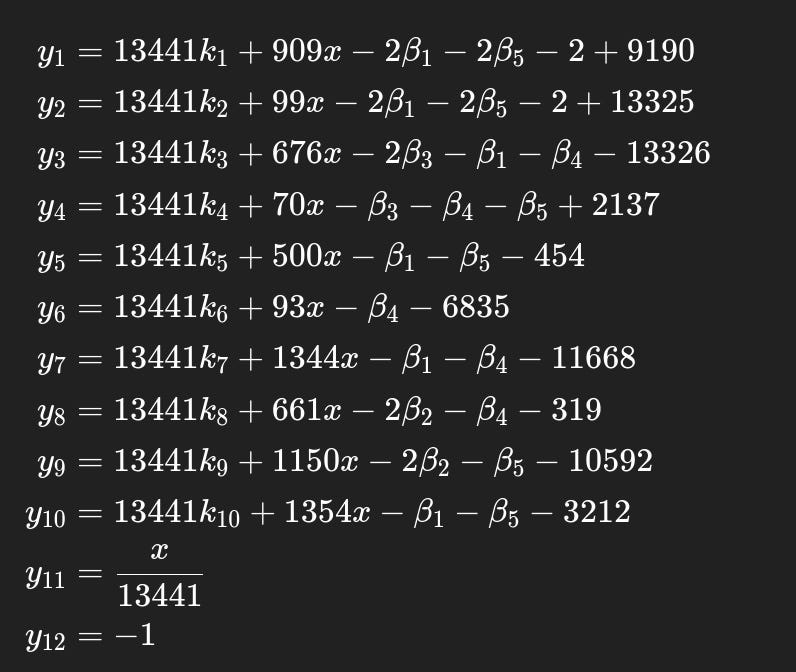
Sanity Check: Observe that the matrix product xB, where B is the HNP-CE lattice from Step 3, generates these linear combinations, and we expect our secret x to appear at the 11th column:
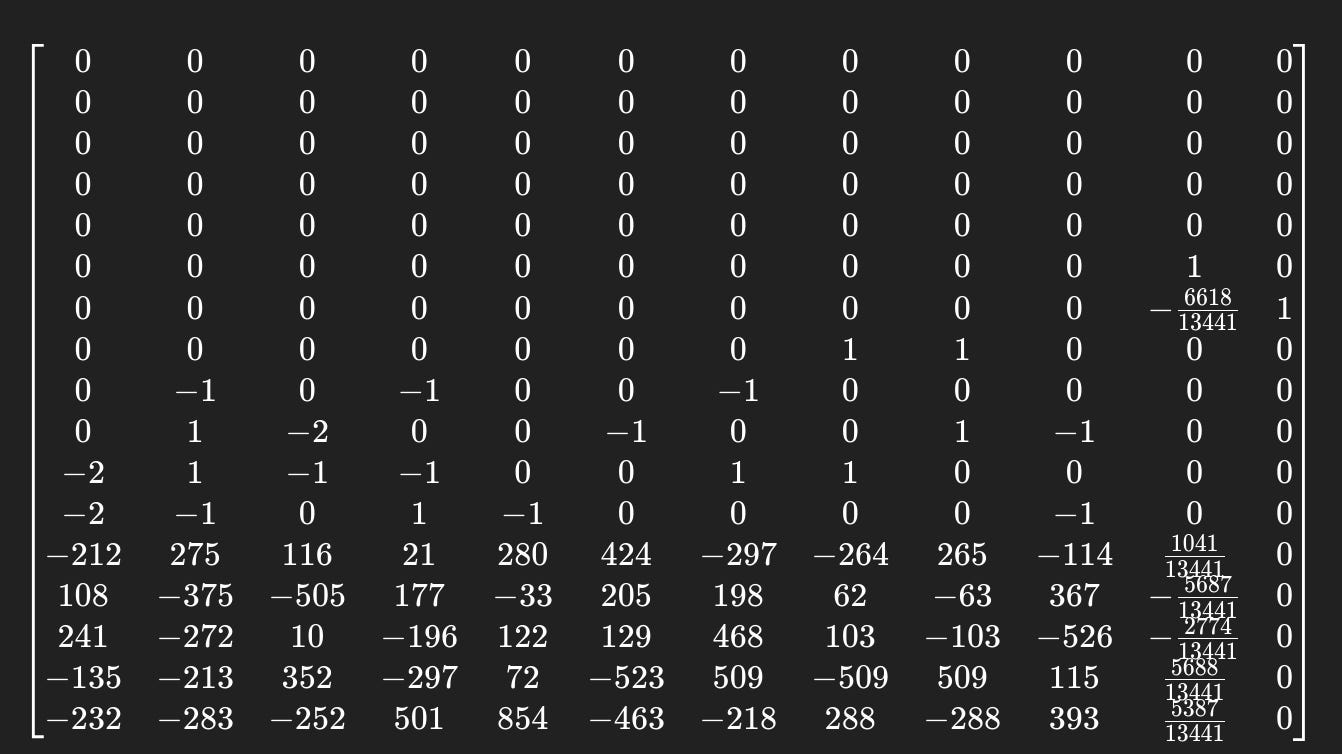
Step 4: Perform LLL reduction on the HNP-CE lattice to obtain:
Step 5: Observe that the secret key (signs ignored) occurs in the row where D=1 occurs in the final column:
We found 6618. It worked lol.
3.0 Possible Improvements
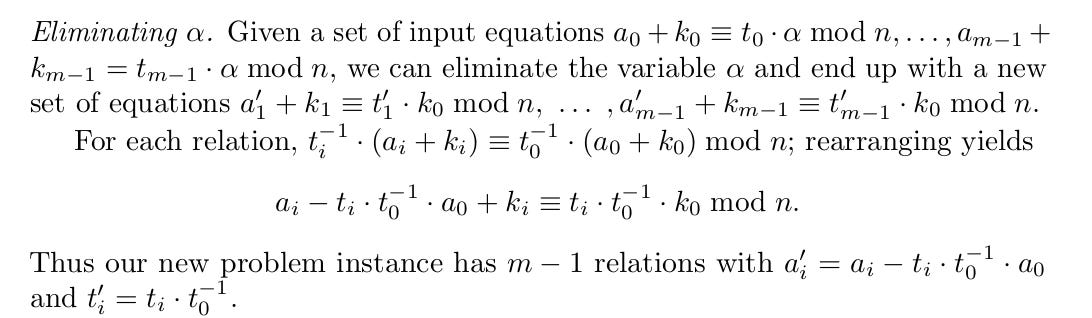
One can borrow the ‘eliminate secret key’ trick from (Albrecht & Heninger, 2020)3 to reduce lattice dimension by 1:
References
Surin, J., & Cohney, S. (2023). A Gentle Tutorial for Lattice-Based Cryptanalysis. University of Melbourne. Cryptology ePrint Archive. PDF Link.
Boneh, D., & Venkatesan, R. (1996). Hardness of Computing the Most Significant Bits of Secret Keys in Diffie-Hellman and Related Schemes. In: Koblitz, N. (eds) Advances in Cryptology — CRYPTO ’96. CRYPTO 1996. Lecture Notes in Computer Science, vol 1109. Springer, Berlin, Heidelberg. https://doi.org/10.1007/3-540-68697-5_11
Albrecht, M.R., & Heninger, N. (2020). On Bounded Distance Decoding with Predicate: Breaking the “Lattice Barrier” for the Hidden Number Problem. IACR Cryptology ePrint Archive.